Check Point: SMB Cyber Security - 600 Appliance Setup, Check Point: Through the Years HD
00:04:19
Обнаружено блокирование рекламы на сайте
Для существования нашего сайта необходим показ рекламы. Просим отнестись с пониманием и добавить сайт в список исключений вашей программы для блокировки рекламы (AdBlock и другие).
Check Point Software Technologies, Ltd. 360 роликов
14798 просмотров на сайте 12n.ru
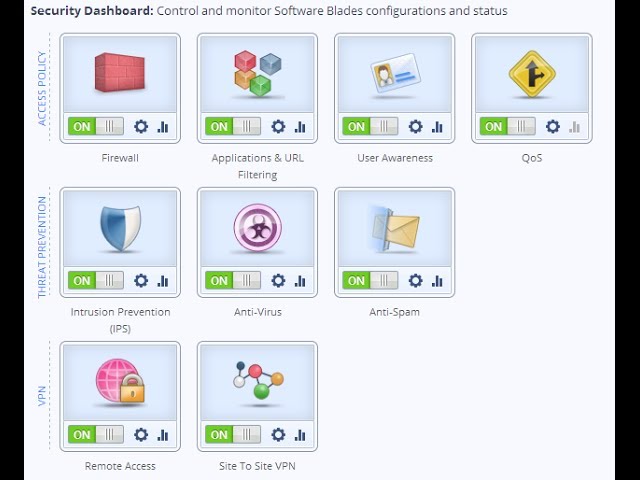
SMB Cyber Security - 600 Appliance Setup.
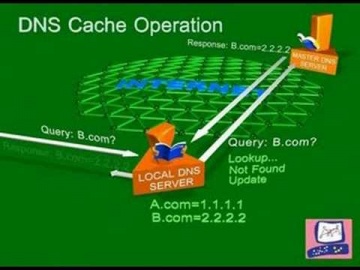
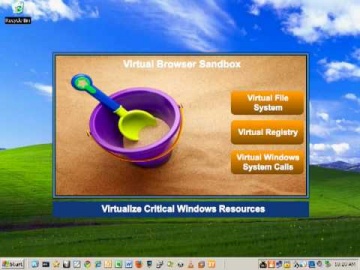
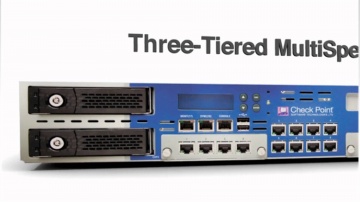
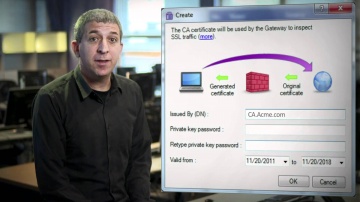
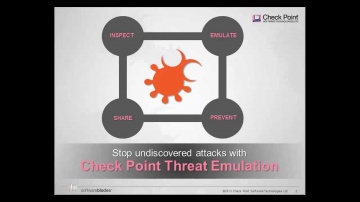
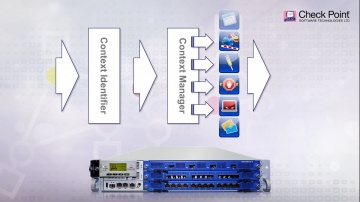
Small businesses need cost-effective security that provides robust protections and ease of use. For more information: brings its long-standing history of security expertise to a range of solutions optimized for the unique demands of small businesses. Few small businesses have money to burn on complex security solutions—or the staff to manage them. Yet, in a world of ever-changing threats, even small businesses need comprehensive, advanced protections against cyber-attacks.Watch our tutorial on how to setup our 600 Appliance, 's latest edition to the product family to protect small businesses against the latest cyber threats.
развернуть свернуть










































Thank you.