Поиск по тегу «sandblast» в разделе Видеокаталог
HD 00:18:09
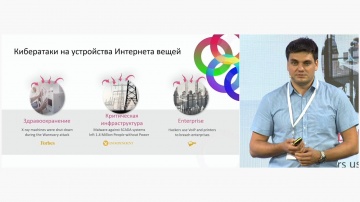
Разработка iot: Эра Интернета вещей. Зачем нужен Check Point NGFW для IoT? - видео
О безопасности IOT рассказывает Дмитрий Кудра, консультант по информационной безопасности Check Point
Cмотреть видео
Cмотреть видео
HD 01:12:00
Что нового в R81 Management?
Никита Турков рассказывает об изменениях и новом функционале в управлении R81 - единой платформе кибезбезопасности.Вопросы, обсуждаемые в этом вебинаре: - Профили Infinity Treat Prevention - Объекты Data Center Query - Новая NAT полит...
Cмотреть видео
Cмотреть видео
HD 00:25:18
Check Point и DevSecOps: безопасность в новой эре разработки ПО
Микросервисы, контейнеры, Kubernetes, DevOps, DevSecOps – эти термины все прочнее входят в нашу жизнь. Даже самые консервативные организации начинают использовать такие технологии. А многие уже в полной мере вкусили их преимущества. Но к...
Cмотреть видео
Cмотреть видео
HD 00:29:35
CloudGuard IaaS: динамическая сетевая безопасность в отечественных и зарубежных облаках - ви
Амир Алиев, консультант по информационной безопасности, Check Point Software Technologies Задействовав ресурсы публичного облака у вас может возникнуть вопрос - где здесь безопасность и кто за нее отвечает? а докладе вы узнаете ответ на эт...
Cмотреть видео
Cмотреть видео
HD 00:27:13
iot: Безопасная экосистема Интернета вещей (IoT) - видео
Do you trust your IoT devices? Itzik Feiglevitch, Product Manager, Check Point Software TechnologiesРастущие с экспоненциальной скоростью устройства Интернета вещей приносят значительную ценность бизнесу, развивая и расширяя его возможности...
Cмотреть видео
Cмотреть видео
HD 00:05:12
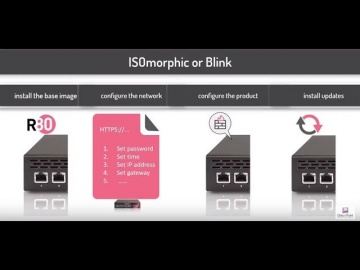
Check Point: Deployment Tools; DIY security appliance images using ISOmorphic
Deployment Tools; DIY security appliance images using ISOmorphic. For more information: In our second video on deployment tools we show you how to image Security Appliances and Open Servers. With the ISOmorphic utility you can inst...
Cмотреть видео
Cмотреть видео
HD 00:21:37
Check Point: Artificial Intelligence: a Silver Bullet in Cyber Security? CPX 360 Keynote
Artificial Intelligence is the Industrial Revolution of our time. It is already reshaping our world and is likely to transform practically every facet of our human lives. Learn more here: Fighting cybercrime is one of its many application...
Cмотреть видео
Cмотреть видео
HD 00:50:38
Check Point: Advanced Cyber Security for 2018 | Introducing 3 New products: Step into Gen-V of Cyber
For more information: is happy to welcome the 5th Generation of Cyber Security with 3 exciting new offerings: Infinity Total Protection (ITP), CloudGuard, and Smart-1 Security Management Appliances. • Infinity Total Protection is a gam...
Cмотреть видео
Cмотреть видео
HD 00:01:54
Check Point: Advanced Cyber Security for 2018 | Prevent 5th Generation Cyber Attacks with Infinity
More information: Infinity is the first consolidated security across networks, cloud and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the future...
Cмотреть видео
Cмотреть видео
HD 00:02:19
Check Point: The Mississippi Secretary of State & CTO Prevents Ransomware
For more information visit Seeking to modernize its security infrastructure, the Mississippi Secretary of State upgraded to SandBlast and now prevents ransomware attacks and enjoys a peace of mind.
Cмотреть видео
Cмотреть видео
HD 00:17:04
Check Point: Advanced Cyber Security for 2018 | Infinity | Technical Deep Dive with Jeff Schwartz
Infinity is the first consolidated security across networks, cloud, and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the future. Jeff Schwartz, our...
Cмотреть видео
Cмотреть видео
HD 00:06:01
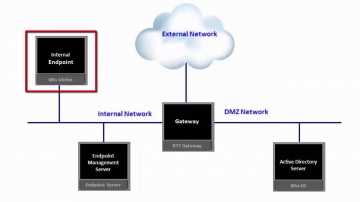
Check Point: Advanced Cyber Security for 2018 - Cyber Security Demo
This video is a technical demonstration of what the cyber security architecture of the future is all about. For more information visit: Infinity is the first consolidated cyber security across networks, cloud and mobile. Unlike other so...
Cмотреть видео
Cмотреть видео
HD 00:01:56
Check Point: Defeats Mobile Cyberattacks
Advanced cybercrimes aren’t science fiction; they’re real – and have real consequences. is at the forefront of mobile security, ensuring that devices and data everywhere remain safe. We don’t just build cutting edge technology: we stand be...
Cмотреть видео
Cмотреть видео
HD 00:02:24
Check Point: SandBlast Mobile: How It Works
Accurate threat detection is a critical component of preventing advanced attacks on smartphones and tablets. Traditional mobile anti-virus, signature-based solutions identify known threats, but they can't detect zero-day malware or apps tha...
Cмотреть видео
Cмотреть видео
HD 00:02:10
Check Point: SandBlast Mobile: Protecting Against Malicious Apps
Our mobile devices are used for both personal and business purposes. Installing new apps may compromise both your private and corporate data. Every year, malicious apps downloaded from official app stores infect millions of mobile devices....
Cмотреть видео
Cмотреть видео
HD 00:02:05
Check Point: Secure your Mobile Phone Now | Introducing SandBlast Mobile
Protecting your enterprise from mobile threats and cyber attacks. More information: Worried about your Mobile Privacy? Secure your mobile phone now against mobile threats. Keeping your business safe from cyberattacks is no easy task, and...
Cмотреть видео
Cмотреть видео
HD 00:01:15
Check Point: Advanced Cyber Attack Business Protection
SandBlast mobile offers the best advanced cyber attack protection for your business. More information: Cybercriminals are better than ever at stealing sensitive information from your smartphone or tablet. Whether it's personal information...
Cмотреть видео
Cмотреть видео
HD 00:07:40
Check Point: [Part 3] Protecting Your Mobile Workforce with SandBlast Mobile & Microsoft Intune
Videos in this Series: Part 1 - Preparing Microsoft Intune for Integration with SandBlast Mobile Part 2 - Configuring Integration between SandBlast Mobile and Microsoft Intune Part 3 - Testing Integration Part 4 - Solution Overview and Star...
Cмотреть видео
Cмотреть видео
HD 00:14:26
Check Point: Protect Your Mobile Workforce with SandBlast Mobile & Microsoft Intune
Videos in this Series: Part 1 - Preparing Microsoft Intune for Integration with SandBlast Mobile Part 2 - Configuring Integration between SandBlast Mobile and Microsoft Intune Part 3 - Testing Integration Part 4 - Solution Overview and Star...
Cмотреть видео
Cмотреть видео
HD 00:10:15
Check Point: Protecting Your Mobile Workforce with SandBlast Mobile & Microsoft Intune Pt.1
Videos in this Series: Part 1 - Preparing Microsoft Intune for Integration with SandBlast Mobile Part 2 - Configuring Integration between SandBlast Mobile and Microsoft Intune Part 3 - Testing Integration Part 4 - Solution Overview and Star...
Cмотреть видео
Cмотреть видео
HD 00:04:12
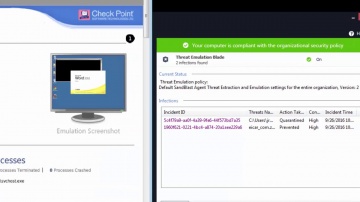
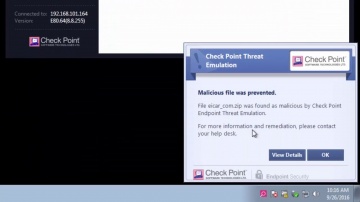
Check Point: SandBlast Agent Protects From Advanced Zero-day Malware
What happens if employees roam outside enterprise network that protect them from advanced zero-day invasions? For more information: SandBlast Agent protects the enterprise end-points from advanced zero-day malware, by using advanced C-P-U...
Cмотреть видео
Cмотреть видео
HD 00:03:41
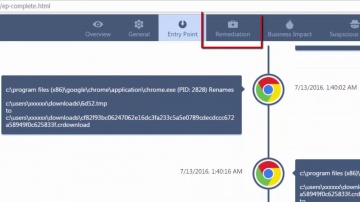
Check Point: Overview of SandBlast Agent Forensics Report | Tech Bytes
This video provides an overview of SandBlast Agent’s Forensics Report. SandBlast Agent defends endpoints and web browsers with a complete set of real-time advanced browser and endpoint protection technologies, including Threat Emulation, T...
Cмотреть видео
Cмотреть видео
HD 00:03:15
Check Point: Installing SandBlast Agent on the Enterprise Endpoint
This video provides an overview of recommended process for deployment of SandBlast Agent on the Enterprise Endpoints. SandBlast Agent defends endpoints with a complete set of real-time advanced endpoint protection technologies, including T...
Cмотреть видео
Cмотреть видео
HD 00:02:35
Check Point: SandBlast Agent Backs Up Anti-Virus by Preventing Recently Discovered Malware | Tech By
What happens if your anti-virus signature database is not updated with a very recently discovered malware? SandBlast Agent defends endpoints with a complete set of real-time advanced endpoint protection technologies, by using the up-to-date...
Cмотреть видео
Cмотреть видео
HD 00:03:59
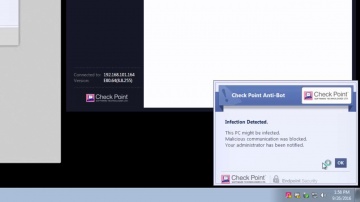
Check Point: SandBlast Agent Anti-Bot Protects the Endpoint from Bot Invasions | Tech Bytes
What happens if employees roam outside enterprise network that protect them from Bot invasions? SandBlast Agent protects the enterprise endpoints from Bot threats, by detecting the communication with command-and-control server. Its Anti-Bot...
Cмотреть видео
Cмотреть видео
HD 00:03:29
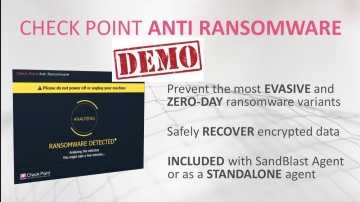
Check Point: Petya Malware Blocked by Anti-Ransomware | Ransomware Cyberattack | Tech Bytes
A massive ransomware attack erupted on June 27 worldwide by a variant of Petya, a form of ransomware that encrypts the entire hard-drive rather than each file individually. This attack by Petya crippled many large banks, government offices ...
Cмотреть видео
Cмотреть видео
HD 00:04:35
Check Point: Anti-Ransomware: Tecnología y Demostración
Anti-Ransomware protege contra el ransomware de día cero. Está incluido en el paquete de SandBlast Agent. Este video presenta la descripción de la solución seguido por una demonstración. Anti-Ransomware usa las habilidades del análisis for...
Cмотреть видео
Cмотреть видео
HD 00:04:00
Check Point: SandBlast Mobile: Quick Start Guide | Tech Bytes
This video is meant to show how easily you can get started protecting your Enterprise's Android and iOS Devices with SandBlast Mobile. More information: Topics covered: Ch1 - Activating Your Admin Account Ch2 - Logging into Your SandBlast...
Cмотреть видео
Cмотреть видео
HD 00:04:30
Check Point: Anti-Ransomware: Solution Brief & Demo | Tech Bytes
Anti-Ransomware protects against sophisticated zero-day ransomware. It is included in SandBlast Agent. More information: Protect endpoints from sophisticated attacks and zero-day threats, enabling a deep understanding of security events f...
Cмотреть видео
Cмотреть видео
HD 00:17:56
Check Point: Hacking the Smartphone | Mobile Cyber Hack Demonstration
Live demonstration of a smartphone hack, from Experience 2017. For more information visit: Watch Michael Shaulov, Head of Mobility Products at Software hack a smart phone in real time. Today every business is a mobile business, with req...
Cмотреть видео
Cмотреть видео













![Check Point: [Part 3] Protecting Your Mobile Workforce with SandBlast Mobile & Microsoft Intune](https://12n.ru/upload/video/images/small/56/3a/563a566e85a82d599192d40f506dd3ff.jpg)