Безопасность
218 роликов  Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных.
Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных.
 Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных.
Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных. Предотвращение утечки данных, DLP
Обеспечение информационной безопасности, борьба с киберпреступностью. ИТ-безопасность.
Layta: Функция слежения TRASSIR ActiveDome
TRASSIR ActiveDome - функция автоматического управления поворотными видеокамерами TRASSIR ActiveDome+, создана как результат тандема двух передовых технологий. Совместная работа технологии объектного трассирования SIMT (Simple Intelligent M...
Cмотреть видео
Cмотреть видео
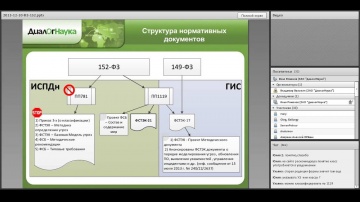
ДиалогНаука: Практические аспекты выполнения требований ФЗ «О персональных данных»
Вебинар на тему: «Практические аспекты выполнения требований ФЗ «О персональных данных» Спикер: Илья Романов, заместитель руководителя Отдела консалтинга, ЗАО «ДиалогНаука»
Cмотреть видео
Cмотреть видео
ДиалогНаука: Тест на проникновение
Вебинар на тему «Практические аспекты проведения теста на проникновение» Спикер: Соколов Андрей Викторович, консультант по информационной безопасности ЗАО «ДиалогНаука»
Cмотреть видео
Cмотреть видео
Cabir: 10 лет первому вирусу для мобильных устройств
15 июня 2004 года специалисты "Лаборатории Касперского" обнаружили первую в истории вредоносную программу для смартфонов. Червь Cabir поражал устройства на базе ОС Symbian и распространялся через Bluetooth. Эксперт "Лаборатории Касперского"...
Cмотреть видео
Cмотреть видео
Лаборатория Касперского: Гид по миру киберугроз - видео
— интерактивная карта киберугроз Где больше спама по утрам — в Германии или в США? Кто чаще кликает на вредоносные ссылки — русские или японцы? Какая страна лидирует по числу заражений? Все это — на нашей интер...
Cмотреть видео
Cмотреть видео
Layta: Видеосервер серии Domination IP MDR в действии
Система видеонаблюдения "Domination" завоевала прочные позиции на российском рынке охранного видеонаблюдения благодаря законченности предлагаемых решений, высокой надежности и производительности работы ОС (Linux) и ПО. Серия Domination IP M...
Cмотреть видео
Cмотреть видео
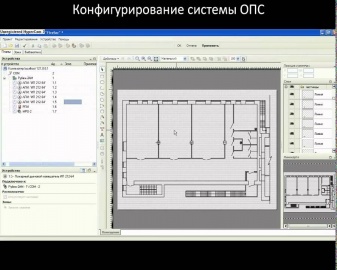
Layta: Адресная система Рубеж - Конфигурация ПО Firesec avi
Для конфигурирования оборудования настройки функционирования и оперативного контроля адресной системы пожарной сигнализации и системы пожаротушения специально разработан программно-аппаратный комплекс «FireSec», который состоит из двух прил...
Cмотреть видео
Cмотреть видео
Layta: Презентация НВП Болид
Научно-внедренческое предприятие «Болид» основано в 1991. Область деятельности - производство и поставка оборудования для систем безопасности, автоматизации и диспетчеризации.
Cмотреть видео
Cмотреть видео
GroupIB: ЕГЭ 2014: Как мошенники в сети зарабатывают на доверчивости школьников
1 канал, программа "Доброе утро" Специалисты Group-IB и журналисты программы "Доброе утро" предупреждают, что мошенники в сети зарабатывают на доверчивости школьников, предлагая ответы на ЕГЭ. Сдать школьный экзамен они не помогут, обойду...
Cмотреть видео
Cмотреть видео
GroupIB: Как скиммеры похищают деньги с банковских карт
Телеканал "Москва 24", выпуск 08.05.2014 Москвичи все чаще сталкиваются с проблемой незаконного обналичивания своих банковских карт. Для этого мошенникам даже не приходится залезать в чужие карманы. О том, кто занимается виртуальным воровс...
Cмотреть видео
Cмотреть видео
GroupIB: Как работают "этичные хакеры"
Москва24, программа «Экономика» от 25.03.2014 Некоторые хакеры взламывают сайты на абсолютно легальных основаниях и получают за это деньги. Речь идет о так называемых "этичных хакерах", которые действуют по контракту с частными компаниями,...
Cмотреть видео
Cмотреть видео
ДиалогНаука: Вебинар. CyberArk
Вебинар на тему: «CyberArk - защита привилегированных учетных записей от внутренних и внешних кибератак» Спикер: Богдан Тоболь, Региональный директор, Восточная Европа/Север, CyberArk
Cмотреть видео
Cмотреть видео
ДиалогНаука: Вебинар. Система предупреждения об утечках конфиденциальной информации и угроз бизнесу
Вебинар на тему: «Система раннего предупреждения об утечках конфиденциальной информации и угрозах бизнесу -- Лавина Пульс» Спикер: Андрей Масалович, Член совета директоров, руководитель направления конкурентной разведки ЗАО «ДиалогНаука»
Cмотреть видео
Cмотреть видео
ДиалогНаука: Вебинар. Комплексные решения Imperva для защиты данных
Вебинар на тему: «Комплексные решения Imperva для защиты данных» Спикер: Николай Кузнецов, старший специалист отдела технических решений ЗАО «ДиалогНаука»
Cмотреть видео
Cмотреть видео
ДиалогНаука: Вебинар. Мониторинг систем SAP с помощью решения agileSI
Вебинар на тему: "Использование решения agileSI для мониторинга информационной безопасности систем SAP" Спикер: Николай Петров, Директор по развитию бизнеса ЗАО "ДиалогНаука"
Cмотреть видео
Cмотреть видео
ДиалогНаука: Виктор Сердюк - о защите информации в России
Выпуск на тему "Защита информации", программа "Капитал", телеканал РБК, Сердюк Виктор Александрович -Генеральный директор ЗАО "ДиалогНаука" 8 июня 2011 г.
Cмотреть видео
Cмотреть видео
ДиалогНаука: Вебинар. Защита информации в соответствии с положением Банка России № 382
Вебинар на тему: «Реализация требований по защите информации в соответствии с положением Банка России № 382» Спикер: Антон Свинцицкий, Руководитель отдела консалтинга ЗАО "ДиалогНаука"
Cмотреть видео
Cмотреть видео
ДиалогНаука: Вебинар. FireEye
Вебинар на тему: «FireEye - система защиты от целенаправленных атак»
Cмотреть видео
Cмотреть видео
ДиалогНаука: Вебинар. Мониторинг событий ИБ на базе HP ArcSight
Вебинар на тему «Практические аспекты реализации мониторинга событий информационной безопасности на базе решений HP ArcSight ESM и HP ArcSight Logger». Спикер: Родион Чехарин
Cмотреть видео
Cмотреть видео
Attention! Hacked Cupid!
Beware Cupid's arrows - sometimes they're malicious Купидон не так безобиден, как кажется! Защити любимых от вирусных стрел. Официальный сайт "Лаборатории Касперского" Читайте нас в социальных сетях: Facebook: Vkontakte: Odnokla...
Cмотреть видео
Cмотреть видео
Веселая песенка о чувствах антивирусного аналитика к вирусописателям
Добрая, милая и трогательная песня антивирусного аналитика "Лаборатории Касперского" о бескрайних, искренних, светлых его чувствах к тем прекрасным людям, что занимаются написанием зловредов. Всем добра! Kind, cute and touchy song of an an...
Cмотреть видео
Cмотреть видео
GroupIB: Компьютерный вирус "Картоха"
Илья Сачков о компьютерном вирусе «Картоха», который помог хакерам похитить данные 110 миллионов пользователей кредитных карт в США
Cмотреть видео
Cмотреть видео
GroupIB: Хакерская атака на камеры видеонаблюдения ГИБДД
В результате хакерской атаки на камеры видеонаблюдения ГИБДД уже несколько суток подряд не работают камеры слежения на дорогах в Подмосковье. Илья Сачков, генеральный директор компании Group-IB, прокомментировал этот инцидент журналистам п...
Cмотреть видео
Cмотреть видео
Как установить Kaspersky Internet Security 2014
При работе в интернете высока вероятность стать жертвой вредоносных программ. Kaspersky Internet Security 2014 защитит ваш компьютер от вирусов, в видео мы расскажем, как установить и активировать Kaspersky Internet Security 2014. Системны...
Cмотреть видео
Cмотреть видео
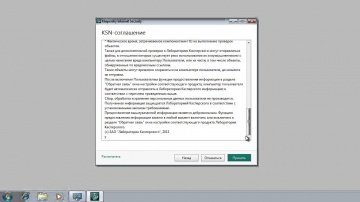
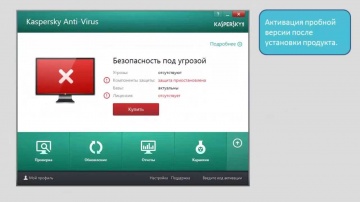
Как активировать пробную версию Kaspersky Anti-Virus 2014?
Чтобы защитить компьютер от вредоносных программ, необходим антивирус. В видео вы узнаете, как активировать пробную версию Kaspersky Anti-Virus 2014, который обеспечит защиту вашему компьютеру бесплатно в течение 30 дней. Видеоинструкции п...
Cмотреть видео
Cмотреть видео
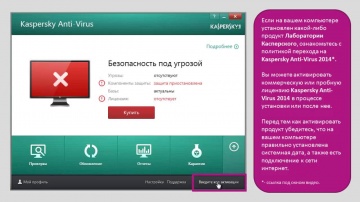
Как активировать Kaspersky Anti-Virus 2014 после установки?
Активация Kaspersky Anti-Virus 2014 после установки. Видеоинструкции по Kaspersky Anti-Virus 2014 . Официальный сайт "Лаборатории Касперского" Читайте нас в социальных сетях: Facebook: Vkontakte: Odnoklassniki: Мой Мир: Goog...
Cмотреть видео
Cмотреть видео
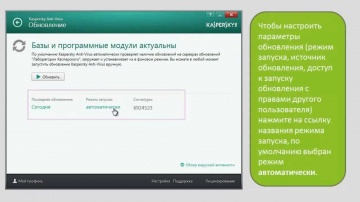
Как обновить антивирусные базы Kaspersky Anti-Virus 2014?
Чтобы защитить компьютер от заражения, необходимо регулярно обновлять антивирусные базы. В видео вы узнаете, как обновить базы Kaspersky Anti-Virus 2014. Видеоинструкции по Kaspersky Anti-Virus 2014 . Официальный сайт "Лаборатории Касперс...
Cмотреть видео
Cмотреть видео
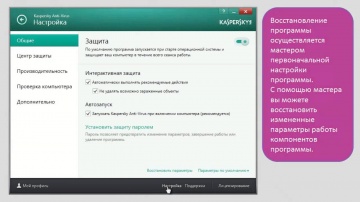
Как восстановить настройки по умолчанию Kaspersky Anti-Virus 2014?
Параметры по умолчанию в Kaspersky Anti-Virus считаются оптимальными и рекомендованы специалистами Лаборатории Касперского. В видео вы узнаете, как вернуть первоначальные настройки Kaspersky Anti-Virus 2014, если вы внесли в них изменения. ...
Cмотреть видео
Cмотреть видео
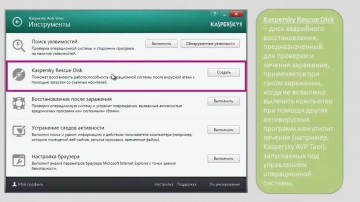
Как использовать Инструменты в Kaspersky Anti-Virus 2014?
Мы расскажем, как в Kaspersky Anti-Virus 2014 использовать Поиск уязвимостей, Диск аварийного восстановления и другие Инструменты. Видеоинструкции по Kaspersky Anti-Virus 2014 . Официальный сайт "Лаборатории Касперского" Читайте нас в ...
Cмотреть видео
Cмотреть видео
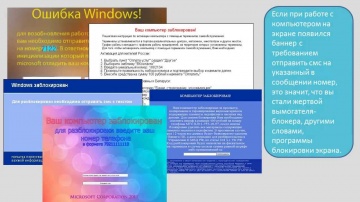
Как защититься от блокеров с помощью Kaspersky Anti-Virus 2014?
В интернете очень легко стать жертвой блокеров, программ-вымогателей. В видео мы расскажем, как Kaspersky Anti-Virus 2014 поможет избежать блокеров. Видеоинструкции по Kaspersky Anti-Virus 2014 . Официальный сайт "Лаборатории Касперского"...
Cмотреть видео
Cмотреть видео