Безопасность
218 роликов  Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных.
Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных.
 Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных.
Data Loss Prevention - DLP - ПО для предотвращения утечек конфиденциальной информации/данных. Предотвращение утечки данных, DLP
Обеспечение информационной безопасности, борьба с киберпреступностью. ИТ-безопасность.
Check Point: CISO viewpoint on modern IT: Britney Hommertzheim, Director, Information Security, AMC
In this session, Britney Hommertzheim, Director, Information Security. AMC Theatres. will share his vision on modern IT, among others the importance of compliance and security and how they are very different. Additionally, he will review ...
Cмотреть видео
Cмотреть видео
Check Point: Gil Shwed Keynote: Stepping Up to Gen V of Cyber Security
Gil Shwed's keynote from CPX 2018 on the future of Cyber Security. Find out what Gen V Cyber Attacks are and how you can prevent the next Cyber Attack. For more information visit -
Cмотреть видео
Cмотреть видео
Check Point: Cloud Security - VMware & CloudGuard - CPX 360 2018
Businesses that use the public cloud are vulnerable to cyber threats. Learn how to close the security gaps in the cloud. Public and hybrid cloud adoption is exploding among enterprises, but so are cloud hacks and breaches. Cloud asset...
Cмотреть видео
Cмотреть видео
Check Point: Information Security : Gioacchino Buscemi (CPX 360)
In this session, Gioacchino Buscemi, Network Security Officer, European Space Agency. will share his vision on modern IT, among others the importance of compliance and security and how they are very different. Additionally, he will review ...
Cмотреть видео
Cмотреть видео
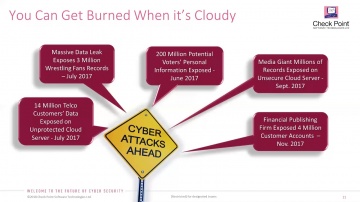
Check Point: Cloud Security Challenges by Peter Sandkuijl - CPX 360 2018
Public and hybrid cloud adoption is exploding among enterprises, but so are cloud hacks and breaches. Cloud assets are at risk from the same types of threats targeting physical networks. What's more, cyber criminals are using increasingly...
Cмотреть видео
Cмотреть видео
Check Point: Artificial Intelligence: a Silver Bullet in Cyber Security? CPX 360 Keynote
Artificial Intelligence is the Industrial Revolution of our time. It is already reshaping our world and is likely to transform practically every facet of our human lives. Learn more here: Fighting cybercrime is one of its many application...
Cмотреть видео
Cмотреть видео
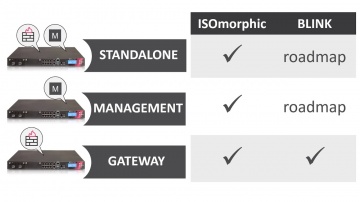
Check Point: Deployment Tools - ISOmorphic & Blink
Deploying Next Generation Firewalls just got easier with the introduction of the Blink utility. For more information: Blink creates a working snapshot of a cleanly installed security gateway with a completed First-Time Configuration Wizard...
Cмотреть видео
Cмотреть видео
Check Point: Happy International Women's Day 2018
The women of share the best advice they ever received in recognition of International Women's Day 2018. Learn more about at
Cмотреть видео
Cмотреть видео
Check Point: Webinar replay – Auto-scale advanced security for Microsoft Azure
For more information visit: Webinar replay - hear from customer George Dialectakis, IT Consultant at Eversource Energy, on how they leverage CloudGuard IaaS advanced threat prevention security for their Microsoft Azure cloud environme...
Cмотреть видео
Cмотреть видео
Check Point: Advanced Cyber Security for 2018 | Introducing 3 New products: Step into Gen-V of Cyber
For more information: is happy to welcome the 5th Generation of Cyber Security with 3 exciting new offerings: Infinity Total Protection (ITP), CloudGuard, and Smart-1 Security Management Appliances. • Infinity Total Protection is a gam...
Cмотреть видео
Cмотреть видео
Check Point: Advanced Cyber Security for 2018 | Prevent Gen V Cyber Attacks with Infinity
More information: ... Infinity is the first consolidated security across networks, cloud and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the fut...
Cмотреть видео
Cмотреть видео
Check Point: Malware Protection 2018 - Public Health Service Prevents, Not Just Detects, Advanced Th
For more information: Malware Protection in 2018 is about prevention not just detection. As a leading West Coast provider of emergency health services, this Public Health Service organization has over two million patients and runs over...
Cмотреть видео
Cмотреть видео
Check Point: Advanced Cyber Security for 2018 | Prevent 5th Generation Cyber Attacks with Infinity
More information: Infinity is the first consolidated security across networks, cloud and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the future...
Cмотреть видео
Cмотреть видео
Check Point: The Mississippi Secretary of State & CTO Prevents Ransomware
For more information visit Seeking to modernize its security infrastructure, the Mississippi Secretary of State upgraded to SandBlast and now prevents ransomware attacks and enjoys a peace of mind.
Cмотреть видео
Cмотреть видео
Check Point: What is CheckMates?
For more information: A brief introductory video about 's official user community: CheckMates!
Cмотреть видео
Cмотреть видео
Check Point: Deploy Small Business Appliances with the Zero Touch Cloud Service
Watch our overview of the Zero Touch Cloud Service to see how you can save valuable time in the initial deployment of our small business security appliances. For more information:
Cмотреть видео
Cмотреть видео
Check Point: Advanced Cyber Security for 2018 | Infinity | Technical Deep Dive with Jeff Schwartz
Infinity is the first consolidated security across networks, cloud, and mobile, providing the highest level of threat prevention against both known and unknown targeted attacks to keep you protected now and in the future. Jeff Schwartz, our...
Cмотреть видео
Cмотреть видео
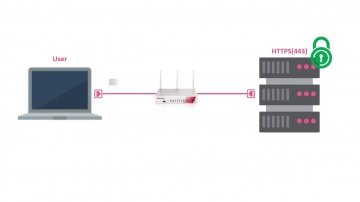
Check Point: HTTPS Inspection on Small Business Appliances
Watch our tutorial on how to enable HTTPS inspection on our 700 Appliance to improve your small business security. More information:
Cмотреть видео
Cмотреть видео
Check Point: Trial Threat Emulation on Small Business Appliances
Watch our tutorial on how to trial Threat Emulation (sandboxing) on our 700 Appliance URL for more information:
Cмотреть видео
Cмотреть видео
Check Point: CAN News, Colin Pennan talks on 'Advanced Persistent Threats'
For More Information Visit: Advanced Persistent Threats are not your average cyber-threat . Learn what makes "Advanced Persistent Attacks" unique and the intricate planning goes into these targeted attacks. In this interview Colin P...
Cмотреть видео
Cмотреть видео
Check Point: Research Finds AliExpress Vulnerability: How It Works
To Read The Full Story Visit: Researchers at discovered that criminals have a new way to trick online shoppers via the massively popular AliExpress shopping portal using Java Script. After discovering the vulnerability, they immediate...
Cмотреть видео
Cмотреть видео
Check Point: R80.10 Logs and Monitor Pane – Key Components and Operations video
In this movie, we elaborate on the key components and operations of events management and reporting, within ’s R80.10 suite.
Cмотреть видео
Cмотреть видео
GroupIB: Threat Intelligence rated by Gartner, IDC, Forrester
Prevent cyber attacks with Threat Intelligence — an effective tool to counter against targeted attacks and data breaches as well as effectively manage information security risks. Group-IB is a leading cyber threat intelligence provide...
Cмотреть видео
Cмотреть видео
Check Point: Migrating from R77.3O to R80.10 Using Advanced Upgrade Procedure
This video demonstrates advanced upgrade of a real customer database from R77.30 to R80.10.
Cмотреть видео
Cмотреть видео
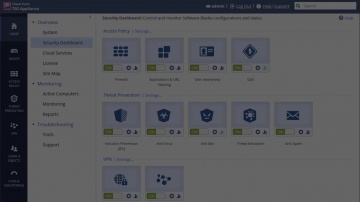
Check Point: Advanced Cyber Security for 2018 - Cyber Security Demo
This video is a technical demonstration of what the cyber security architecture of the future is all about. For more information visit: Infinity is the first consolidated cyber security across networks, cloud and mobile. Unlike other so...
Cмотреть видео
Cмотреть видео
Check Point: SandBlast Prevents Ransomware at the Mississippi Secretary of State
Learn more about how SadBlast helped Mississippi's Secretary of State here: The Mississippi Secretary of State was spending a lot of time remediating attacks on the endpoint. Seeking to enhance endpoint security, the agency adopted Sand...
Cмотреть видео
Cмотреть видео
Check Point: SandBlast Prevents Ransomware at the Mississippi Secretary of State
Learn more about how SadBlast helped Mississippi's Secretary of State here: Concerned about mounting advanced threats, the mississippi Secretary of state adopts SandBlast. Just 2 days after deployment, SandBlast prevents a ransomware at...
Cмотреть видео
Cмотреть видео
Check Point: Upgrading from R77.3O to R80.10 Via CPUSE
This video demonstrates in-place upgrade of a real customer database from R77.30 to R80.10 via CPUSE interface in the Web UI.
Cмотреть видео
Cмотреть видео
Check Point: Denham Capital Enjoys Agility and Security in the vSEC Protected Microsoft Azure Cloud
More information: A leading private equity firm with great success in the often unpredictable energy industry, Denham Capital needed to move to the cloud for increased agility without compromising security. With Microsoft Azure and vSEC ...
Cмотреть видео
Cмотреть видео
Check Point: Denham Capital Secures Cloud, Gains Visibility
More information: A leading private equity firm with great success in the often unpredictable energy industry, Denham Capital needed to move to the cloud without compromising performance or security. With vSEC, Denham found a solution to...
Cмотреть видео
Cмотреть видео