Check Point Software Technologies, Ltd.

360 роликов
Нет подписчиков
Компания Check Point Software Technologies Ltd. — мировой поставщик решений в области обеспечения интернет-безопасности, единственный поставщик средств обеспечения полной безопасности Total Security для сетей, данных и конечных узлов, объединенных единой средой управления.
Сортировка

00:00:31
Обнаружено блокирование рекламы на сайте
Для существования нашего сайта необходим показ рекламы. Просим отнестись с пониманием и добавить сайт в список исключений вашей программы для блокировки рекламы (AdBlock и другие).
HD Check Point: Without the Best Security, Bad Things Happen
Two chatty security guards get distracted by a shiny coin, and their VIP client is swept away by criminals in a white van. For more information visit Takes real life security scenario, and demonstrates how the standard, traditional methods just don’t do the job any more. Gen V from , the only solution for 5th generation cyber security.
Check Point: 600 Security Appliance: One Box, Complete Protection | SMB Cyber Security
Learn more about the 600 appliance: The 600 provides a complete security package with firewall, VPN, antivirus, intrusion prevention and more, at a price your small business can afford.
Cмотреть видео
Cмотреть видео
Check Point: Preventing Tomorrow's Cyber Security Threats
Increasing your enterprise security often means increasing your complexity and management challenges in kind. For more information, visit Growing complexity in security infrastructure puts a huge strain on the efficiency of the security o...
Cмотреть видео
Cмотреть видео
Check Point: Stopping The Next Cyber Attack | Threat Prevention
Understanding your exposure to threats—and what you can do about it is not only responsible business management—it’s critical to business survival. Turn Security into an Enabler, Not a Disabler. offers network infrastructure security, ant...
Cмотреть видео
Cмотреть видео
Check Point: Customer Success Video: Hotel Nikko San Francisco
Hotel Nikko relies on its network to support guest services, reservation systems, property management and other critical business operations. Keeping the network safe and secure is key, and even a brief outage means lost revenue, disappoin...
Cмотреть видео
Cмотреть видео
Check Point: Identifying The Best Sandboxing Solution Featuring Miercom | Advanced Threat Prevention
Learn More: Protecting against known, and new, advanced, unknown threats requires the most rapid and precise detection and protection technologies. With multiple solutions available, finding the best one can be challenging. Independent te...
Cмотреть видео
Cмотреть видео
Check Point: Employee Testimonial - Why work at ?
If you are passionate about innovation, dream of working with the brightest, thrive in a fast-paced, changing and challenging environment – see what we have to offer. Career opportunities: Employee, Kellmen Meghu, describes why Software ...
Cмотреть видео
Cмотреть видео
Check Point: RSA Conference 2014 - Partner Insights - Avnet
Learn More: Gimv, a leading European private equity and venture capital investment company, leverages ThreatCloud Emulation technology to prevent against zero day attacks. Watch as IT Manager Kristof Poppe discusses his experience wi...
Cмотреть видео
Cмотреть видео
Check Point: Customer & Partner Insights- FishNet Security
Learn More: speaks with customers and partners at RSA Conference 2014 in San Francisco. Watch as they share what makes them a fan.
Cмотреть видео
Cмотреть видео
Check Point: RSA Conference 2014 - Customer Insights - Securities America, Inc.
Find out more: speaks with customers and partners at RSA Conference 2014 in San Francisco. Watch as Leon Johnson from Securities America, Inc. speaks about the critical need to secure data in the financial industry and how integrates ...
Cмотреть видео
Cмотреть видео
Check Point: RSA Conference 2014 - Customer Insights - Leidos
Find out more: speaks with customers and partners at RSA Conference 2014 in San Francisco. Watch as Joseph Royal of Leidos shares what makes him a fan.
Cмотреть видео
Cмотреть видео
Check Point: RSA Conference 2014 - Partner Insights - Dataway
Find out more: speaks with customers and partners at RSA Conference 2014 in San Francisco. Watch as Heather Zalatimo from partner Dataway shares thoughts about 's superior management capabilities and what makes her a fan.
Cмотреть видео
Cмотреть видео
Check Point: RSA Conference 2014 - Partner Insights - Soluciones Seguras
Find out more: speaks with customers and partners at RSA Conference 2014 in San Francisco. Watch as Eli Fashka of Soluciones Seguras shares how they are using solutions with their customers. He also speaks to 's management and consol...
Cмотреть видео
Cмотреть видео
Check Point: Customer Quote: Uncovered Potential Risks with Security Checkup
Gimv IT Manager Kristof Poppe comments on 's Security Checkup report and how it influenced their decision to go with .
Cмотреть видео
Cмотреть видео
Check Point: Customer Quote: ThreatCloud Emulation Discovers and Prevents Zero-Day Attacks
Gimv IT Manager Kristof Poppe comments on 's Threat Emulation and zero day attacks.
Cмотреть видео
Cмотреть видео
Check Point: Customer Quote: ThreatCloud Emulation Integrated into Software Blade Architecture
Gimv IT Manager Kristof Poppe comments on 's ThreatCloud Emulation integrated into the Software Blade Architecture for layered security.
Cмотреть видео
Cмотреть видео
Check Point: Customer Quote: Industry Leading NGFW Performance with Integrated Management
Gimv IT Manager Kristof Poppe comments on 's industry leading next generation firewall performance with integrated management.
Cмотреть видео
Cмотреть видео
Check Point: Threat Emulation Protects Investment Firm: Gimv
Learn More: Gimv, a leading European private equity and venture capital investment company, leverages ThreatCloud Emulation technology to prevent against zero day attacks. Watch as IT Manager Kristof Poppe discusses his experience wi...
Cмотреть видео
Cмотреть видео
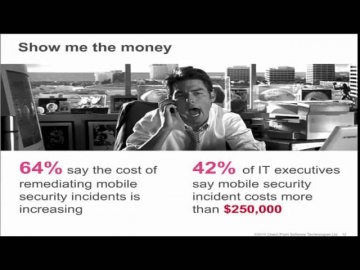
Check Point: The Security Zone Ep. 5: Impact of Mobile Devices on Information Security
teamed up with Dimensional Analysis to survey over 700 IT and security professionals in 6 countries to learn the current attitudes and trends regarding the impact of mobile devices on information security.
Cмотреть видео
Cмотреть видео
Check Point: The Security Zone Ep. 2: Forget Zero Day, Hello Zero Second
Delayed response is no longer enough to protect your business from the speed of malware. We need a ZERO SECOND response. A recent benchmark test assessed how fast Threat Emulation and other competitive products stop malware from entering a...
Cмотреть видео
Cмотреть видео
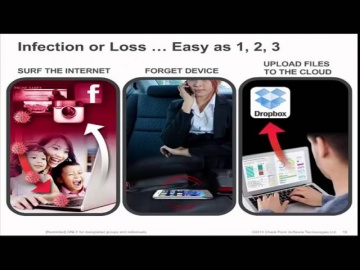
Check Point: The Security Zone Ep. 4: Bridge the Enterprise Mobile Security Gap
Mobile security continues to be a challenge for organizations providing business access on mobile platforms, whether it is on corporate owned or personal devices. While point products provide help with addressing some concerns, they do not ...
Cмотреть видео
Cмотреть видео
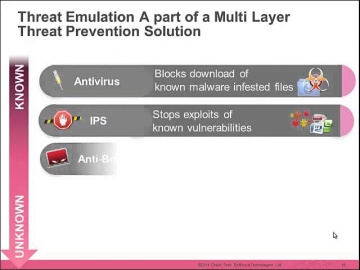
Check Point: The Security Zone Ep. 3: How to Choose Your Next Generation Threat Emulation Solution
Organizations are facing unprecedented growth in the number of security threats from malware. New attack types combine known and unknown threats to exploit vulnerabilities. Join us to learn how can protect against unknown malware.
Cмотреть видео
Cмотреть видео
Check Point: Customer Success: AlmavivA Group
Almaviva, Italy's number one Information & Communication Technology provider, describes how Technologies protects the organizations infrastructure.
Cмотреть видео
Cмотреть видео
Check Point: Malware Threat Prevention | Zero-Day, Zero-Second.
What can malware do in 60 seconds? One minute can change everything for a business. So what happens when the speed of business is overtaken by the speed of malware? The team devised a test to quantify that exact question. Learn More: As ...
Cмотреть видео
Cмотреть видео
Check Point: Capsule Docs – Keep Your Business Documents Protected | Enterprise | Network Security
Capsule Docs protects your sensitive business documents to ensure they don’t get unintentionally exposed. See how Capsule Docs works to provide document security.
Cмотреть видео
Cмотреть видео
Check Point: Capsule Docs - Secure Business Documents Everywhere | Network Security
Capsule Docs ensures that only authorized individuals can access your business documents. Confidently share documents with coworkers, business partners, clients, and vendors, because you are in control of their access and sharing rights.
Cмотреть видео
Cмотреть видео
Check Point: Mobile Security: Capsule
Introducing Capsule – Your Complete Secure Mobility Solution. Learn More: Only provides ONE solution that addresses ALL your mobile security needs: Protect devices (smartphones, tablets, and laptops) from threats everywhere, establish a...
Cмотреть видео
Cмотреть видео
Check Point: The Security Zone Ep. 1: Unknown 300 | Enterprise Cyber Security
In recent benchmark testing, 300 malicious files were scanned through Threat Emulation and other competitive products. The results found that outperformed all of the others.
Cмотреть видео
Cмотреть видео
Check Point: Globb TV interview: Amnon Bar-Lev
President Amnon Bar-Lev discusses the big business of today’s cybercrimes
Cмотреть видео
Cмотреть видео
Check Point: Sky News Interview with Kurt Hansen
Software Technologies Ltd. — крупнейший в мире поставщик в области безопасности. Компания предлагает покупателям ведущие в индустрии решения и защищает покупателей от кибератак с непревзойденным уровнем успешного обнаружения вре...
Cмотреть видео
Cмотреть видео